
Supporting Your Strategy and Operations with Certifications
Supporting Your Strategy and Operations with Certifications In last month’s blog, we explored the challenges of sustaining a GRC program

Supporting Your Strategy and Operations with Certifications In last month’s blog, we explored the challenges of sustaining a GRC program

Breaking Silos: Converging Compliance and Operational Programs In many organizations, compliance and operational programs have evolved as distinct entities. This

Sustainable Controls: The Missing Link in GRC Program Success Why do so many GRC programs struggle to operate as intended

The Strategic Value of Process Mapping In today’s complex and fast-paced cybersecurity landscape, the strategic value of process mapping may

The Versatility of NIST CSF In today’s dynamic threat landscape, organizations require structured, adaptable, and measurable approaches to cybersecurity and
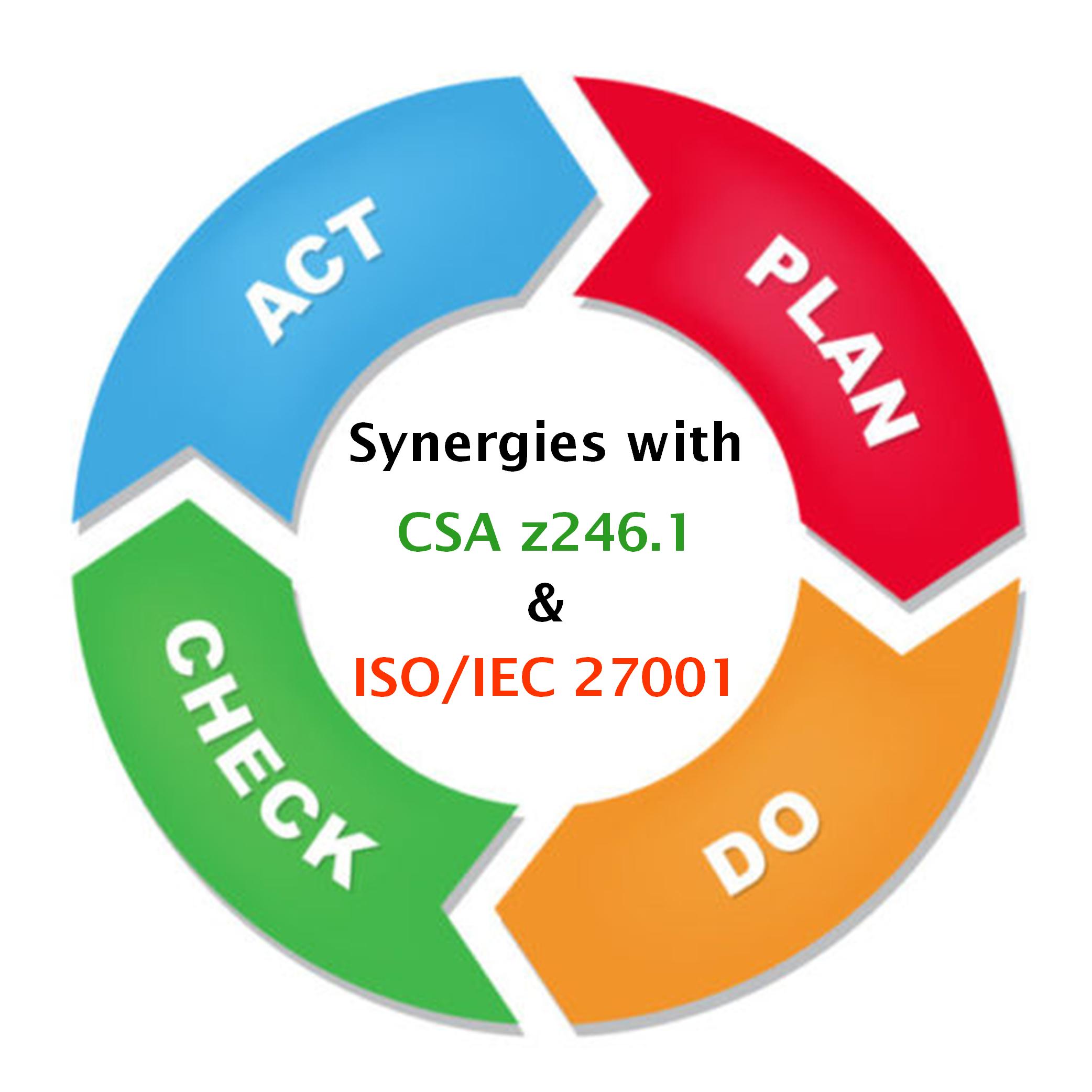
Synergies Between CSA z246.1 and ISO 27001 As of May 31, 2025, CSA Z246.1 will be in effect in Alberta,

In today’s competitive job market, the value of professional certifications have become increasingly important. They are meant to serve as