In today’s complex and fast-paced cybersecurity landscape, the strategic value of process mapping may be seen as a necessary evil — time-consuming, resource-intensive, and sometimes undervalued. But when approached strategically, it becomes a powerful tool for aligning operations with business objectives, optimizing resource allocation, and reducing risk exposure.
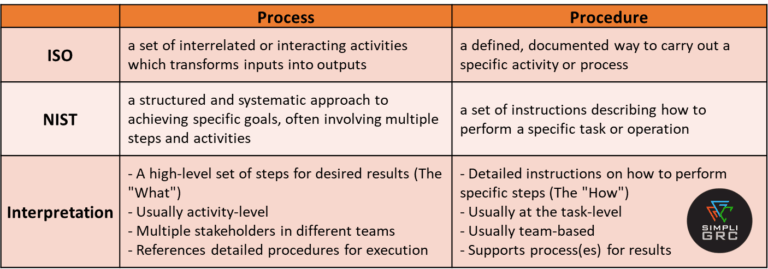
Before diving into the value of process mapping, it’s important to clarify what we mean by a “process.” Organizations often tailor definitions to fit their internal culture unless bound by regulatory or authoritative standards. Below is a simplified distinction between a process and a procedure, drawing from ISO and NIST frameworks:
Processes can take many forms — flowcharts, documented narratives, or undocumented tribal knowledge. Regardless of format, authorized processes should support the organization’s strategic goals and value chain. Key questions to consider include:
The Govern function, introduced in CSF 2.0, plays a pivotal role by anchoring the framework in organizational context, risk tolerance, and strategic objectives. This ensures that cybersecurity efforts are aligned with business goals and stakeholder expectations.

Consider a familiar scenario: a meeting with diverse stakeholders is held and someone whiteboards a concept to explain a challenge. That visual representation often becomes the catalyst for shared understanding, problem-solving, and actionable next steps. Process maps serve a similar purpose — bridging communication gaps, breaking down silos, and aligning teams around a common operational vision.
Some of the key benefits of process mapping include:
Despite these advantages, many organizations struggle to implement process mapping consistently. Why? It requires time, skilled resources, and sustained leadership support. In high-pressure environments, subject matter experts (SMEs) are often too busy delivering results to document their workflows. But what happens if that SME leaves the organization or wins the lottery?
The risk isn’t hypothetical, it’s operational. Without documented processes, organizations face increased exposure to knowledge loss, inefficiencies, and compliance gaps.
Moreover, rigid processes can interfere with innovation. That’s why process mapping should be viewed as a dynamic, evolving practice, not a one-time exercise. When supported by leadership, it enables cost transparency and data-driven decision-making. For example, if “Process #123” consumes 60% of an SME’s time and relies on “Tool ABC” for “Use Case XYZ”, leadership can quantify the cost and explore optimization or automation opportunities.
To embed process mapping into your organization’s DNA, leadership buy-in is essential. Whether it’s part of a formal business case or an embedded cultural practice, the goal is the same: to drive operational excellence through visibility and control.
Process maps can serve as a baseline for:
Each of these areas can be expanded into its own strategic initiative. The key is to tailor the approach to your organization’s unique goals, risk appetite, and maturity level.
At SimpliGRC, we understand that process mapping is more than a compliance checkbox, it’s a strategic enabler. Our services are designed to help cybersecurity and risk leaders operationalize process management in a way that’s scalable, sustainable, and aligned with business outcomes.
Whether you’re looking to reduce risk, improve efficiency, or prepare for audits, we can help you assess the value of process mapping in your environment and build a roadmap for success.
Curious how process mapping can enhance your cybersecurity posture or optimize your GRC operations? Let’s talk. Contact SimpliGRC to explore how we can support your team with tailored solutions that deliver measurable impact.
#simpligrc #processmanagement #processmapping #valuechain